03 Nov

Introduction:
Security is now one of the core topics any architect or DevOps take into consideration when designing and building a web hosting environment, with internet expansion, it’s becoming very normal to receive DDOS attacks for different goals, like attempting of stealing your website data, or using your environment like a basement for attacking other websites, or just for the sake of bringing your environment down!
As a leading cloud provider, AWS has taken this into consideration by providing many services to secure your application, AWS is committed to secure theirs under layer infrastructure like networking, storage. however, it’s your responsibility to address and mitigate security issues on your account.
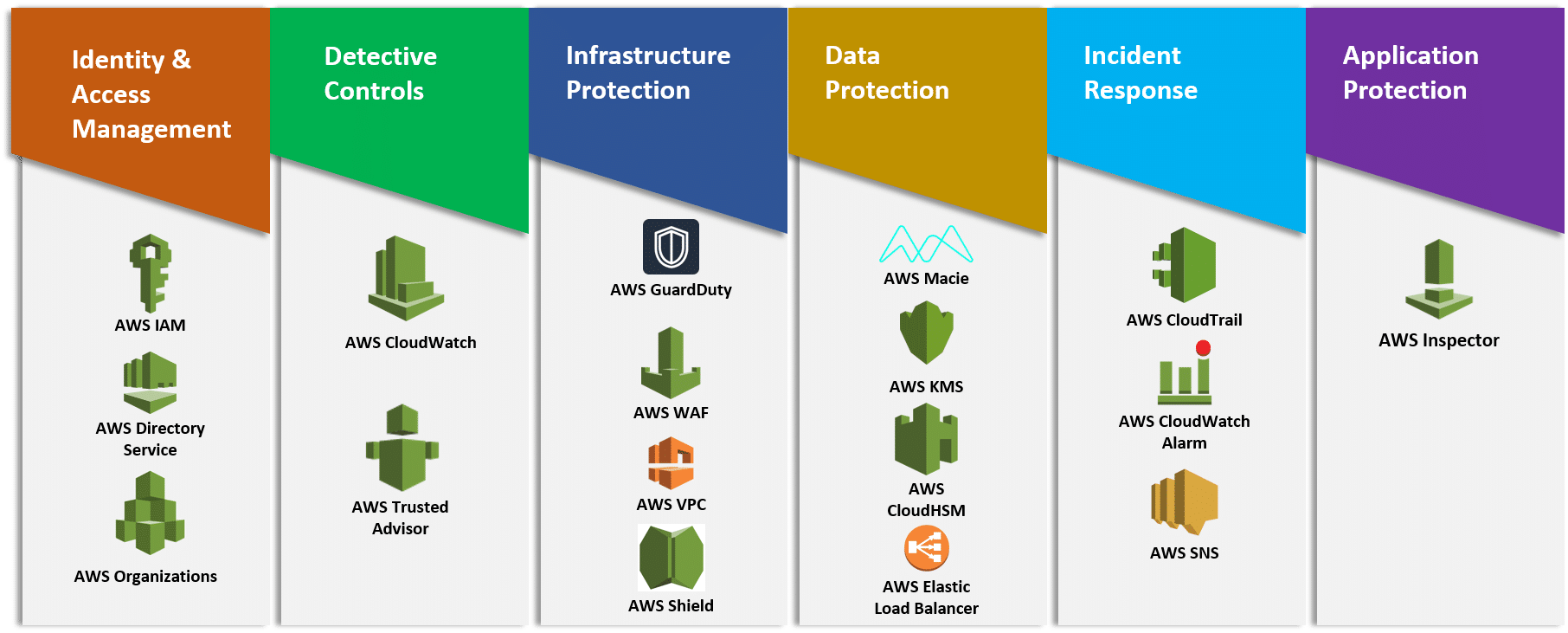
AWS Services:
we’re going to discuss some of the services that AWS provide to prevent your website from DDOS attacks:
Roue 53:
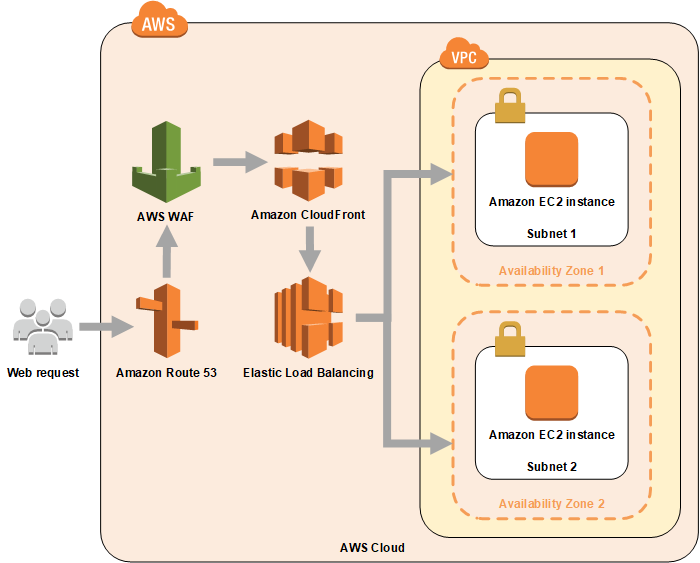
Yes, Route53 is DNS management service, however, AWS makes sure to provide security tools from the first step the attacker trying to attack your website, which is DNS resolving:
One of the most common targets of DDoS attacks is the Domain Name System (DNS). Amazon Route 53 is a highly available and scalable DNS service designed to route end users to infrastructure running inside or outside of AWS. Route 53 makes it possible to manage traffic globally through a variety of routing types and provides out-of-the-box shuffle sharding and Anycast routing capabilities to protect domain names from DNS-based DDoS attacks.
Cloudfront:
Traffic routed through CloudFront are inspected inline. Always-on monitoring, anomaly detection, and mitigation against common infrastructure DDoS attacks such as SYN/ACK floods, UDP floods, and reflection attacks are built into both Route 53 and CloudFront.
AWS Shield:
With AWS Shield Standard you get always-on heuristics-based network flow monitoring and inline mitigation against common, most frequently occurring network and transport layer DDoS attacks. AWS Shield Advanced provides enhanced resource-specific detection and employs advanced mitigation and routing techniques for sophisticated or larger attacks. You also get 24×7 access to the AWS DDoS Response Team (DRT) for manual mitigation of edge cases affecting your availability. AWS Shield Advanced also provides visibility and insights into all your DDoS incidents through AWS CloudWatch metrics and attack diagnostics. Finally, you can also see the DDoS threat environment on AWS with the Global threat environment dashboard.
AWS WAF:
A WAF or Web Application Firewall helps protect web applications by filtering and monitoring HTTP traffic between a web application and the Internet. It typically protects web applications from attacks such as cross-site forgery, cross-site-scripting (XSS), file inclusion, and SQL injection, among others. A WAF is a protocol layer 7 defense (in the OSI model) and is not designed to defend against all types of attacks. This method of attack mitigation is usually part of a suite of tools that together create a holistic defense against a range of attack vectors.
Autoscaling:
Despite the autoscaling feature is built for increasing resources on-demand to improve cost and availability, it helps a lot in DDOS mitigation, by responding to high traffic spikes caused by DDOS attacks, and instead of having your environment going down until DDOS attack is dedicated by the above security services, your website environment will resist by increasing the instances to handle the traffic. once DDOS attack is identified the attack will be blocked and scaled instances will be terminated.
Security Groups & NACLs:
with security groups, you can block ports not needed or specify the source of the traffic, for example, you can specify that HTTP and HTTPS traffic can only be accepted through your load balancer.
Networks Access Lists are useful when responding to DDoS attacks because it can allow you to create your own rules to mitigate the attack if you know the source IP addresses or other signature. You can use network ACLs in conjunction with AWS WAF ACLs.
Conclusion:
AWS provides and comprehensive list of features to protect your website and web application from a DDOS attack, we highly recommend you also to read this whitepaper which can give you more details on how to protect each layer of your request with AWS.